
This book is organized into 13 chapters to help you learn how to best leverage the Elastic Stack for your use cases.
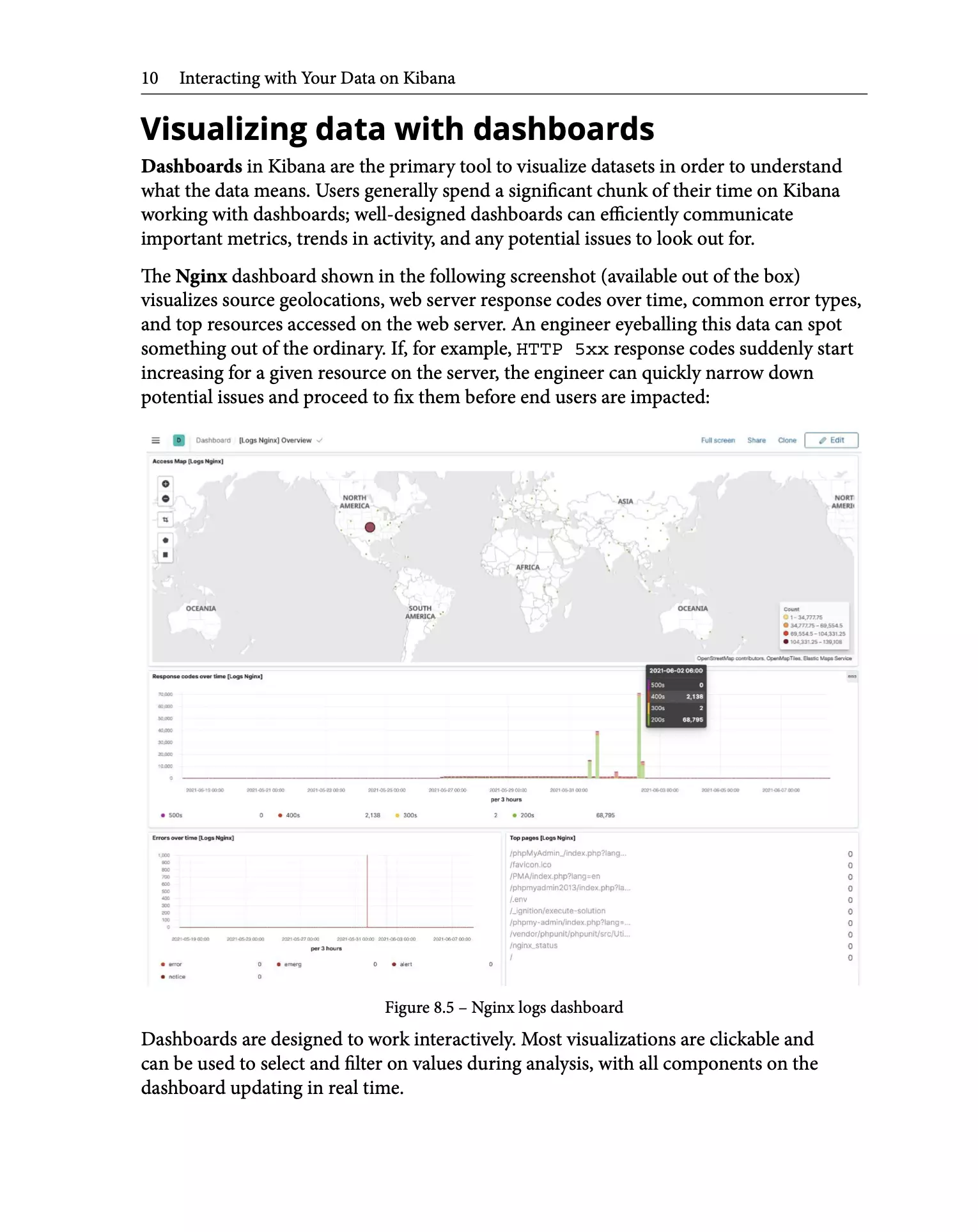
Introduction to the Elastic Stack
Installing and Running the Elastic Stack
Indexing and Searching for Data
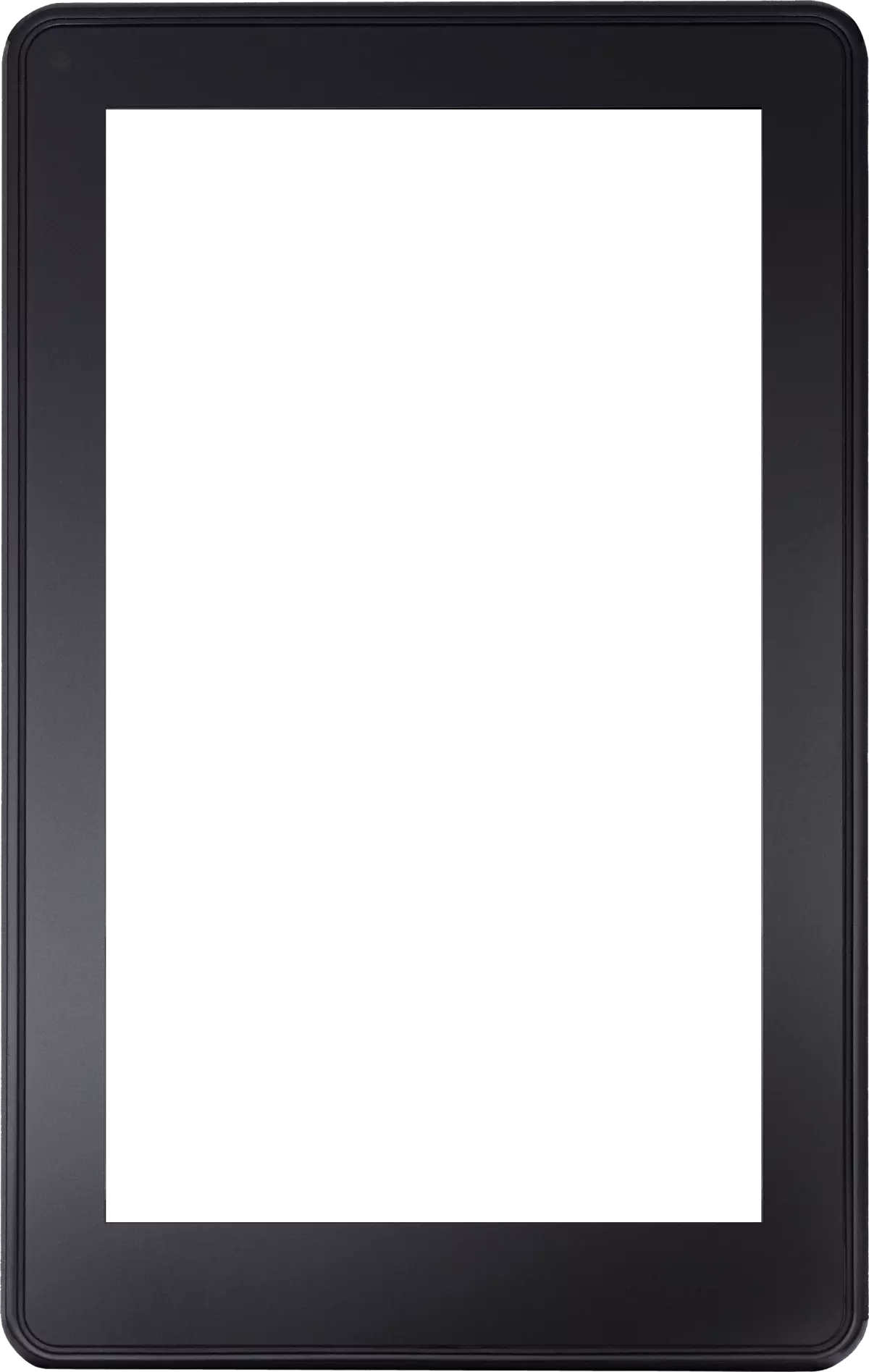
Leveraging Insights and Managing Data on Elasticsearch
Running Machine Learning Jobs on Elasticsearch
Collecting and Shipping Data with Beats
Using Logstash to Extract, Transform, and Load Data
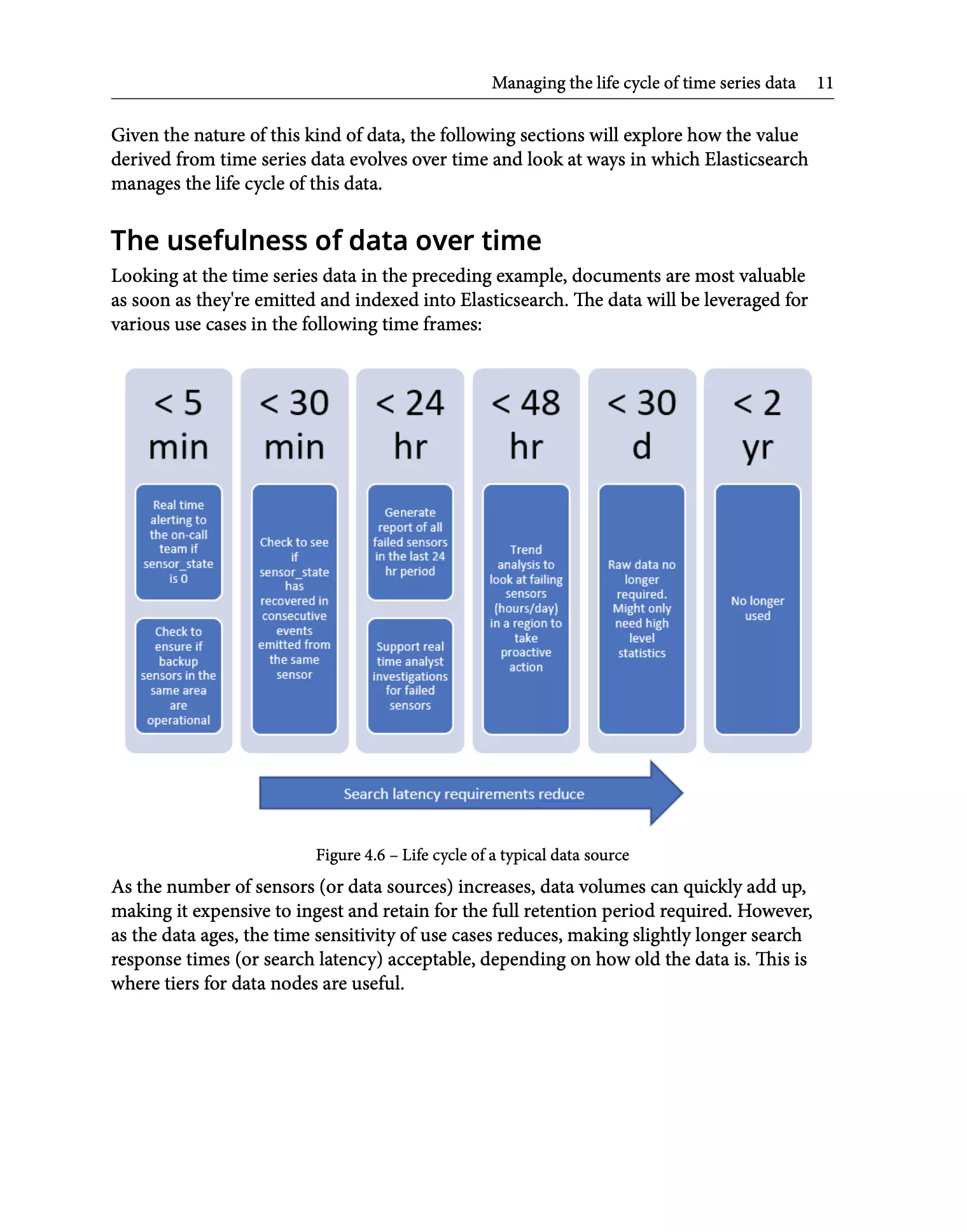
Interacting with Your Data on Kibana
Managing Data Onboarding with Elastic Agent
Building Search Experiences Using the Elastic Stack
Observing Applications and Infrastructure Using the Elastic Stack
Security Threat Detection and Response Using the Elastic Stack
Architecting Workloads on the Elastic Stack

Get your hands on a copy of the book to get started on your journey with the Elastic Stack. Begin with detailed introductions to core technologies, learn from hands-on examples and understand the best practices that you need to adopt to build successful outcomes on the Elastic Stack.
* The Amazon store for your region is automatically displayed for your convenience.